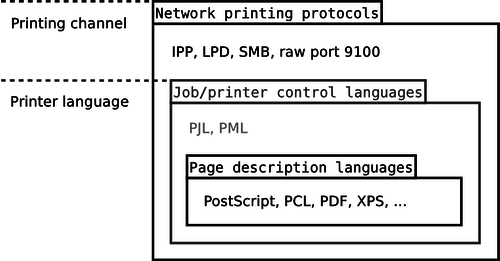
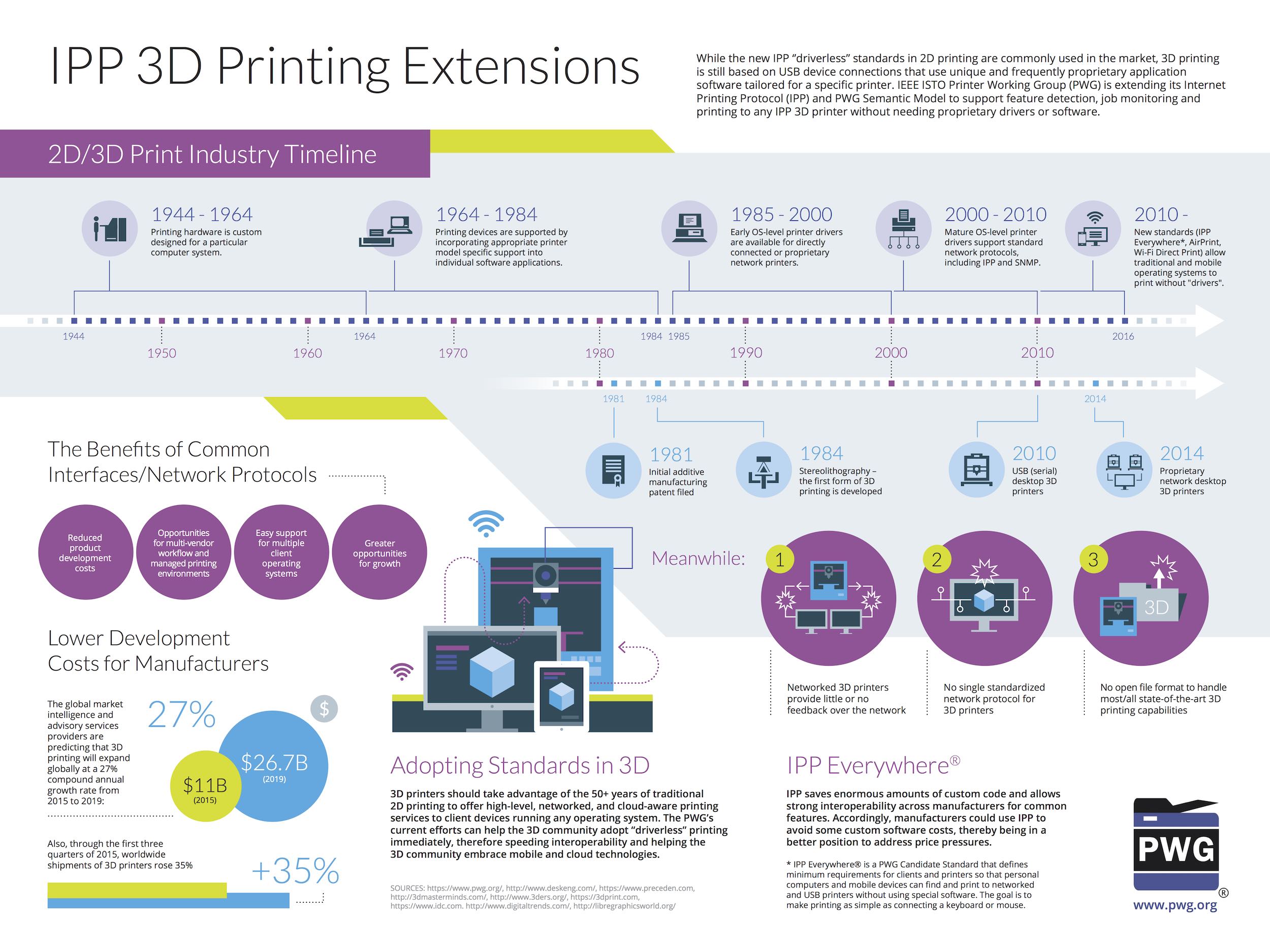
Exploiting and Abusing Printers Remotely - Building Detection Algorithm - WootCloud HyperContext Powered Security
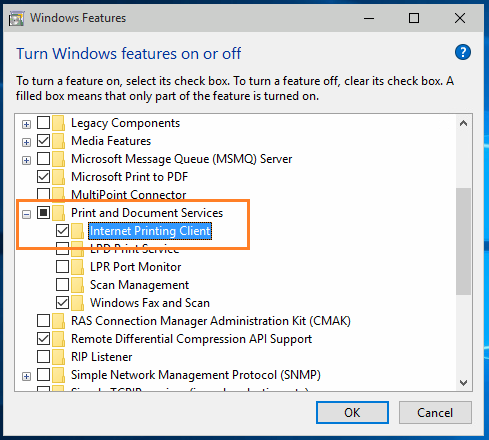
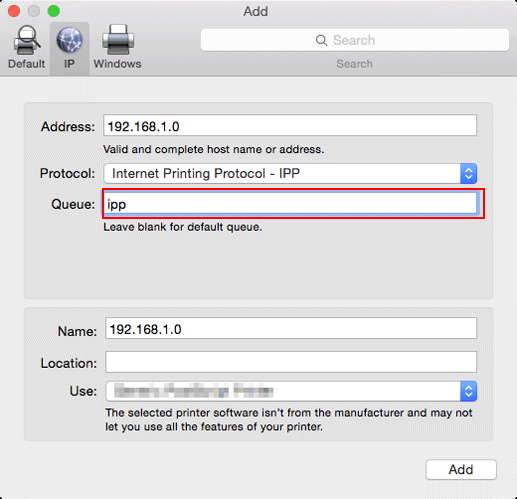
Section 21.2. The Internet Printing Protocol | Advanced Programming in the UNIX Environment, Second Edition (Addison-Wesley Professional Computing Series)